India faces one of the fastest-growing cyber threat landscapes globally. Recent industry studies show that millions of cyberattack attempts target Indian businesses every year — and most attacks now target applications and APIs rather than servers.
Think about it:
We pay via UPI
We order via apps
We authenticate using OTP.
We store documents in DigiLocker.
We run factories via IoT.
So what are attackers attacking?
Not infrastructure. They attack digital behaviour.
This is why modern cybersecurity in India now revolves around three tightly connected pillars:
edge computing
web application firewall
threat hunting
Together, they form the foundation of what security professionals call:
Why Traditional Security Failed in Modern Indian Infrastructure
Earlier security assumed a very simple architecture.
Old Model
User → Internet → Firewall → Server → Database
Today’s Model
User → Mobile Network → CDN → Edge Node → API Gateway → Cloud Microservices → Third-Party APIs → Database
Security broke because:
There is no single perimeter anymore.
What Changed in the Indian Digital Ecosystem
India skipped multiple technological generations — from desktop banking directly to mobile fintech, from paper identity directly to Aadhaar APIs. That leap created massive distributed infrastructure, but security models remained centralized for too long.
Key Changes
Massive mobile-first adoption
Public APIs (UPI, GST, KYC)
SaaS adoption by SMEs
IoT in manufacturing
5G low-latency requirements
Edge-hosted content delivery
Now the attacker doesn’t need to hack a server.
They simply manipulate:
login flows
API logic
tokens
sessions
rate limits
And that is exactly where our three pillars start working together.
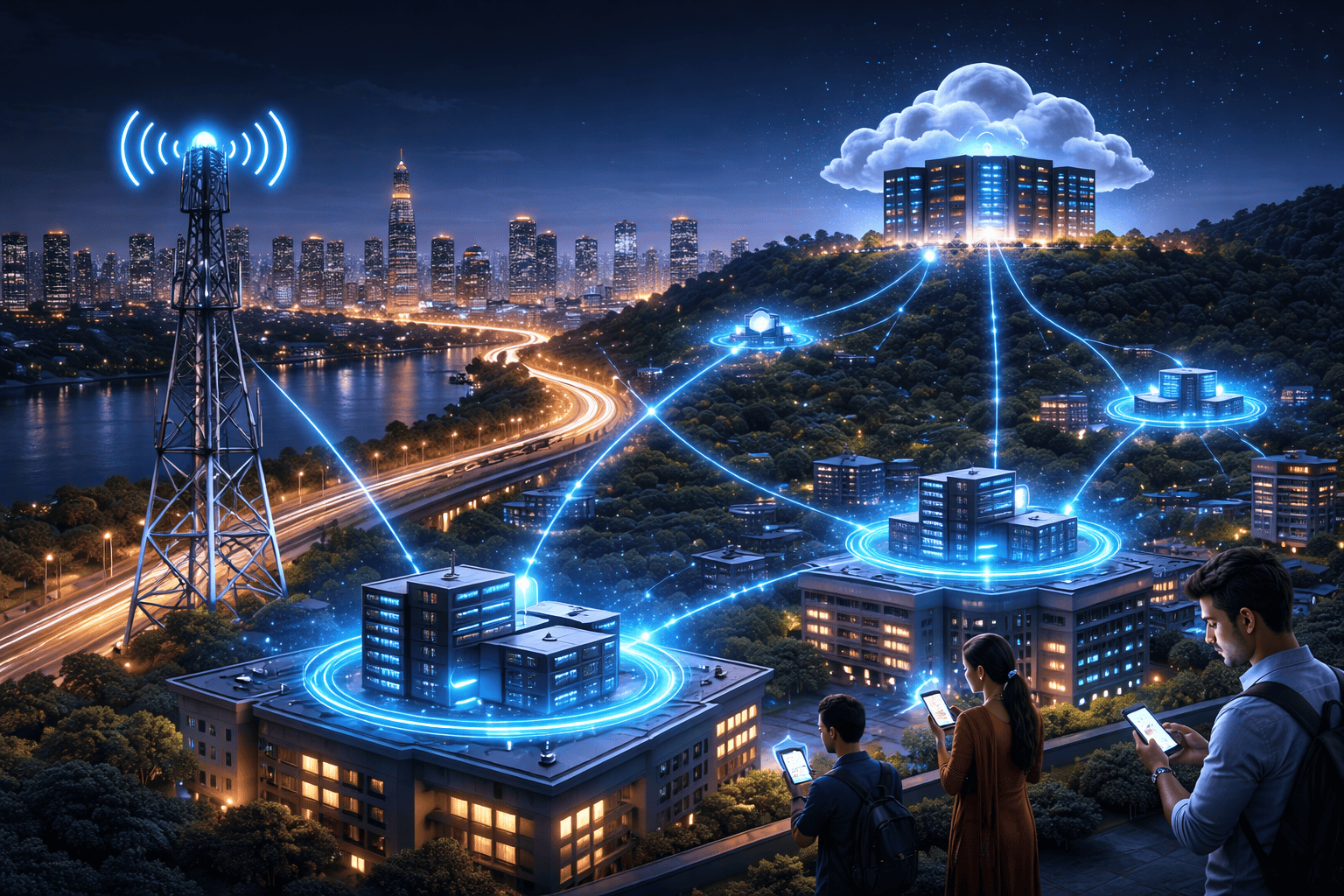
Understanding Edge Computing — Security Begins Near the User
Edge computing processes data physically closer to users instead of routing everything to centralized cloud data centers. In India — where latency, bandwidth cost, and regional connectivity vary drastically — edge architecture is not just performance optimization; it is a security necessity.
When decisions are made near the user, suspicious behaviour can be detected before it reaches core infrastructure.
Why India Specifically Needs Edge Computing
High mobile user density
Tier-2 and Tier-3 connectivity variability
Real-time payment ecosystem
Smart manufacturing adoption
5G network slicing
OTT streaming demand
Security Benefits of Edge Computing
Security tools running centrally only see final requests. But edge nodes see behaviour — the pattern, timing, and anomalies. This allows detection of attacks before they scale.
Security Advantages
Early bot detection
Local anomaly filtering
Reduced DDoS impact radius
Faster response to credential stuffing
API abuse throttling
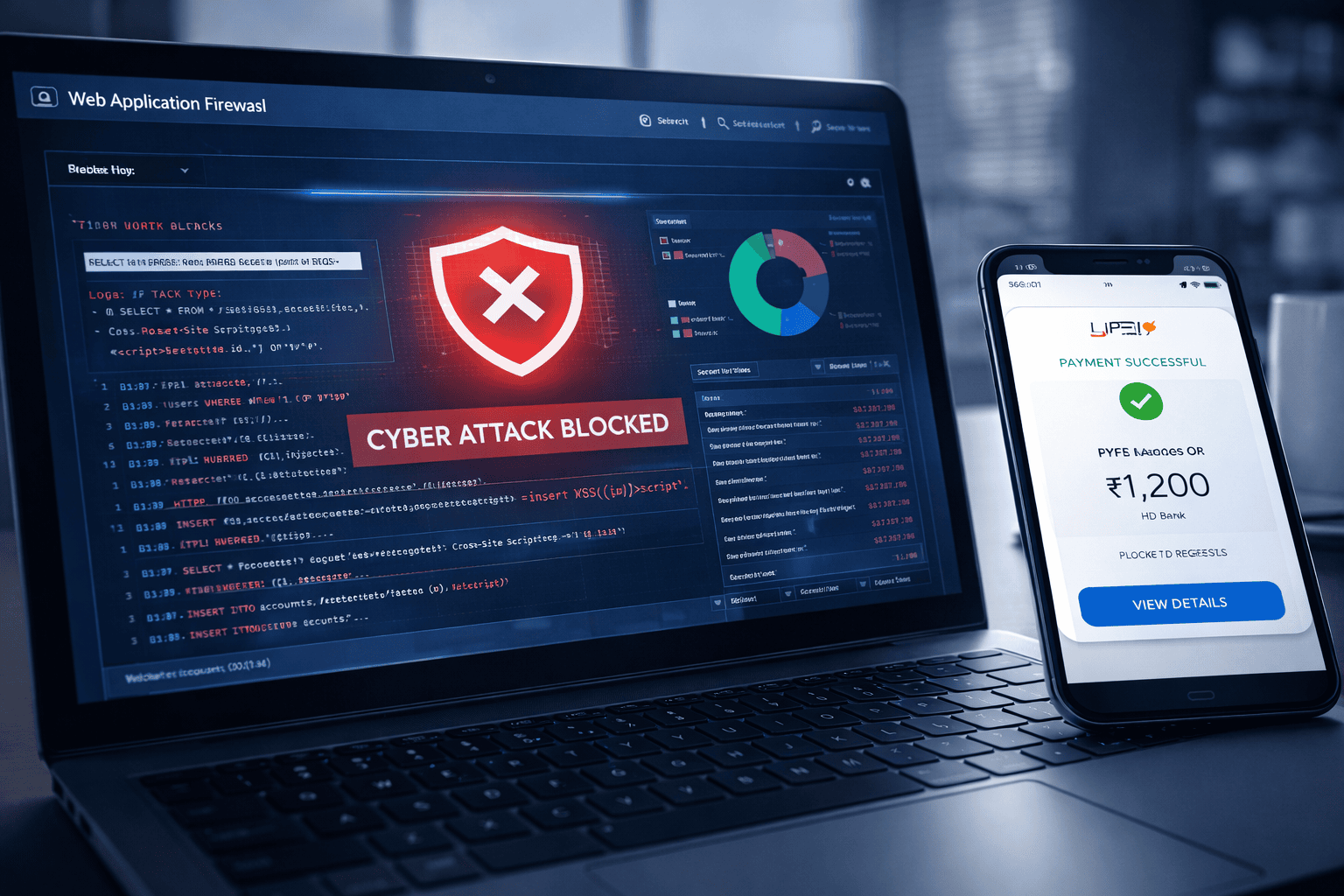
The Role of Web Application Firewall — Protecting the Logic, Not Just the Server
Traditional firewalls protect ports. Modern attacks exploit logic.
This is where a web application firewall becomes essential.
What a WAF Actually Understands
A web application firewall inspects HTTP/HTTPS traffic and understands application behaviour — forms, parameters, cookies, headers, JSON payloads. Instead of blocking an IP, it blocks malicious intent.
Types of Attacks WAF Prevents
SQL Injection
Cross-Site Scripting (XSS)
Remote File Inclusion
API Abuse
Session Hijacking
Bot scraping
Credential stuffing
Why WAF Alone Is Not Enough
A WAF protects against known patterns. But attackers increasingly use low-and-slow techniques and legitimate credentials. That means the traffic looks normal — yet the intention is malicious.
So organizations need a security layer that asks:
“Is this behaviour normal for this user?”
That layer is threat hunting.
Threat Hunting — Moving From Defence to Investigation
Threat hunting is not alert-based security. It is hypothesis-based security.
We do not wait for alarms. We actively search for hidden attackers.
What Makes Threat Hunting Different
Traditional SOC
Threat Hunting
Reacts to alerts
Searches for anomalies
Signature-based
Behaviour-based
Automated
Analyst-driven
Known threats
Unknown threats
Typical Threat Hunting Questions
Security analysts start asking investigative questions instead of waiting for logs to complain.
Examples
Why did this user log in from two cities in 5 minutes?
Why is an API called exactly every 3 seconds?
Why is encrypted traffic unusually large?
Why did a normal user suddenly access admin endpoints?
These patterns bypass WAF — but not threat hunting.
How Edge + WAF + Threat Hunting Work Together
This is the real architecture shift.
Instead of isolated tools, modern Indian enterprises deploy security mesh layers.
Layered Security Flow
Edge computing filters abnormal traffic geographically.
Web application firewall blocks malicious payloads.
Threat hunting investigates suspicious behaviour.
Example — UPI Payment Attack Scenario
An attacker tries automated payment validation attacks.
What Happens
Edge detects abnormal request frequency → throttles.
WAF blocks injection payload attempts
Threat hunting detects a credential enumeration pattern.
The attack stopped before the financial fraud.
Conclusion
India’s digital growth is fundamentally decentralized. Payments, governance, healthcare, and commerce now operate through distributed APIs rather than centralized applications.
Because of that shift, cybersecurity also evolved:
From protecting machines → To protect interactions → To protecting intent.
Edge computing provides visibility, A web application firewall provides protection, and threat hunting provides intelligence.
The organizations that integrate all three don’t just defend systems — they defend trust.
And in a digital economy, trust is infrastructure.
Key Takeaways
Security perimeter no longer exists — behaviour is the new perimeter.
Edge computing stops attacks early.
A web application firewall blocks malicious inputs.
Threat hunting detects unknown attackers.
All three together form modern cyber defence.
Organizations using only one of them remain vulnerable.
FAQ
Q: Is a firewall the same as a web application firewall?
A: No. A traditional firewall protects networks, while a web application firewall protects application logic and HTTP traffic.
Q: Does edge computing replace cloud security?
A: No. It extends security closer to users and reduces the attack surface before reaching cloud systems.
Q: Is threat hunting only for large enterprises?
A: Increasingly no. Managed SOC and MDR services now provide threat hunting to mid-size Indian companies.
Q: Can WAF stop zero-day attacks?
A: Mostly no. That is why behavioural detection through threat hunting is necessary.
Q: Which industry needs this architecture most in India?
A: BFSI, fintech, government platforms, and large e-commerce ecosystems.


