Is Your Organisation Truly Safe in India's Exploding Cybercrime Landscape?
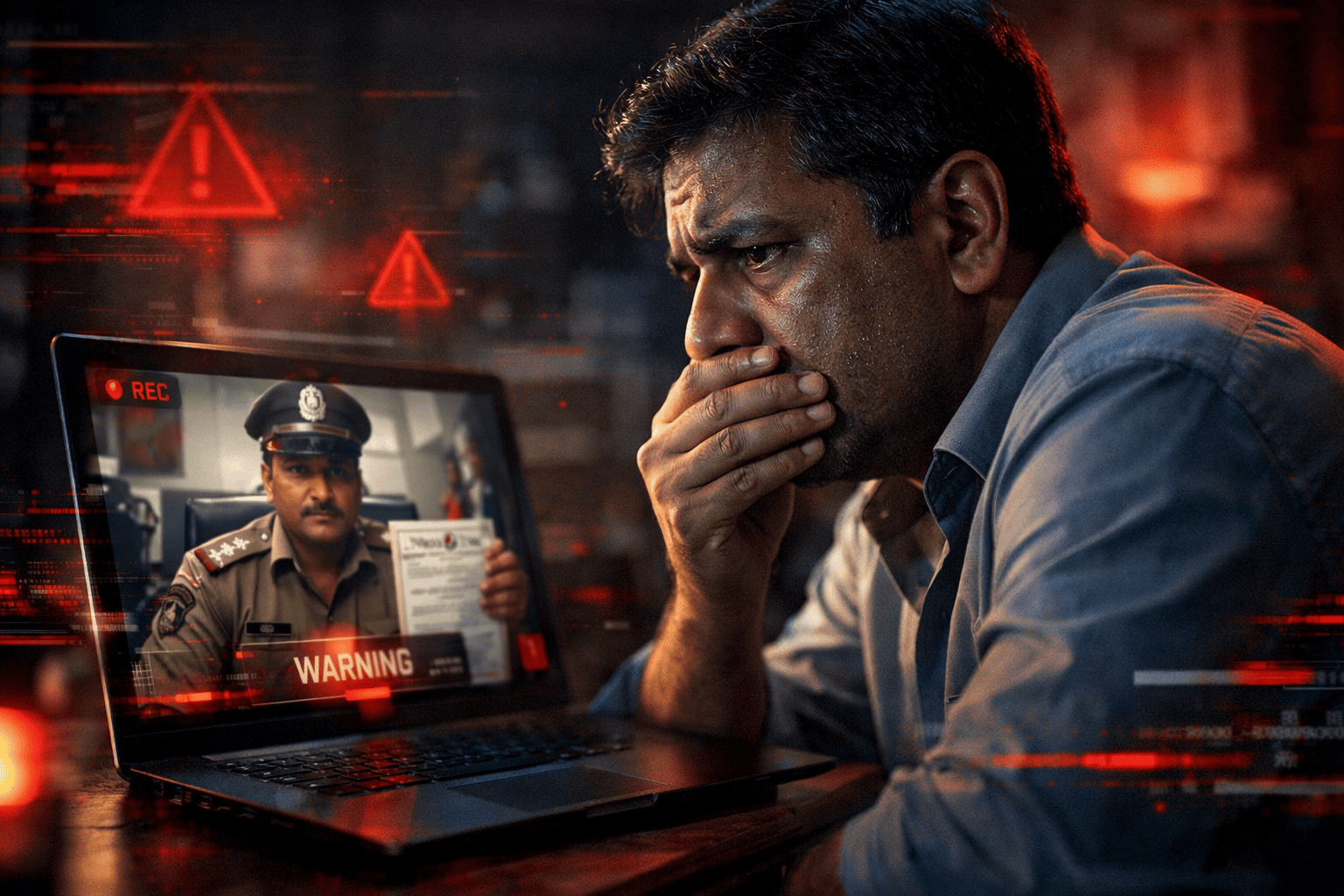
Imagine receiving a video call from someone dressed in a police uniform, seated behind an official-looking desk, telling you that a case has been registered against you for money laundering and that if you move from your screen, you will be arrested immediately. Sounds like a scene from a thriller film, doesn't it? Unfortunately, for thousands of Indians, this terrifying experience is devastatingly real. It is called a 'Digital House Arrest', and it is one of the fastest-growing cybercrime tactics targeting our citizens today.
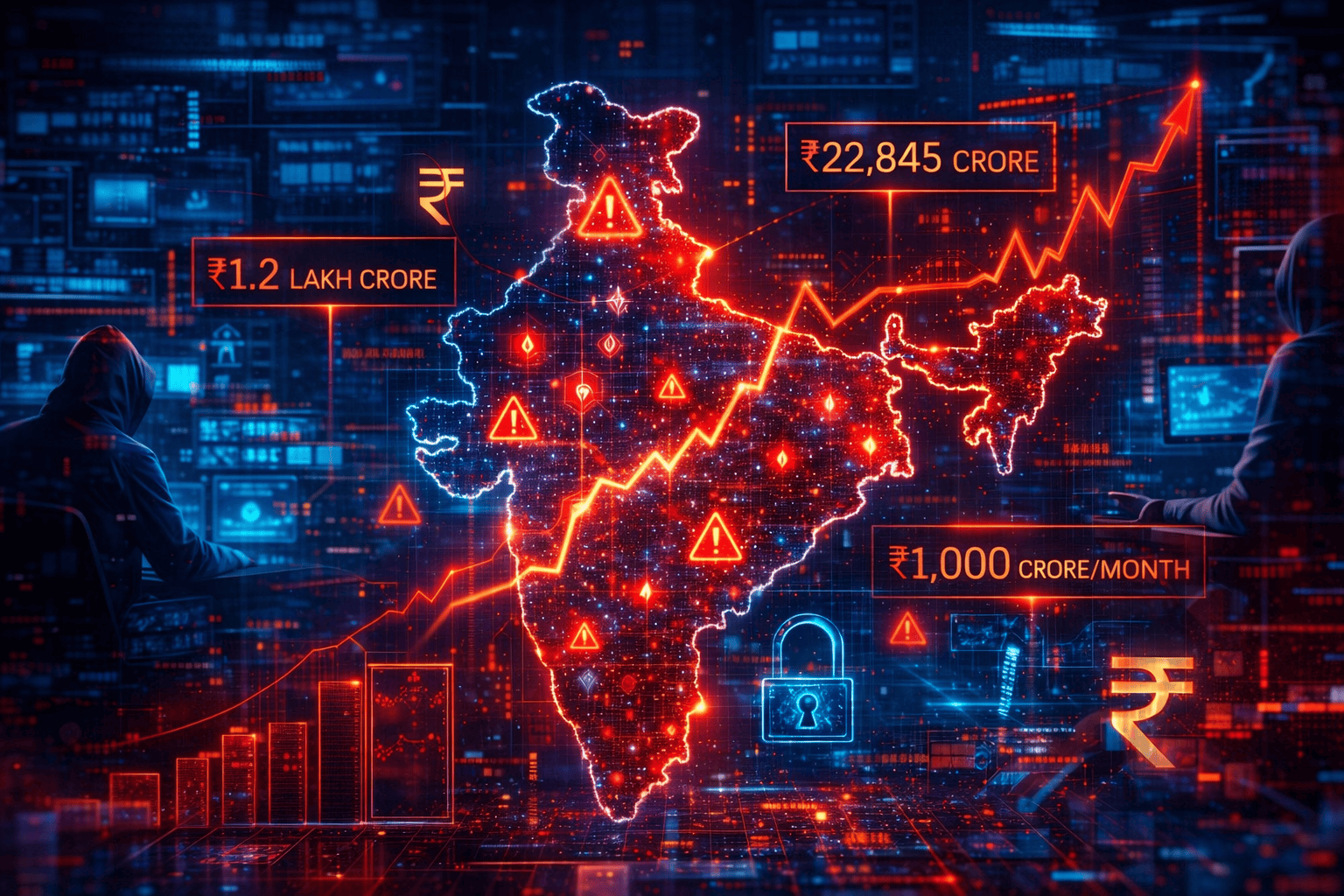
We are living through what experts rightly call India's most dangerous decade for digital security. India reported nearly 22.68 lakh cybercrime incidents in 2024 with financial losses skyrocketing by 206% year-on-year to reach a staggering Rs. 22,845 crore. The I4C projects that by 2025, India may lose over Rs. 1.2 lakh crore to cybercrime, averaging roughly Rs. 1,000 crore lost every single month.
1. The Digital House Arrest Epidemic: How Scammers Are Holding India to Ransom
The 'Digital House Arrest' scam is among the most psychologically sophisticated fraud mechanisms ever deployed against Indian citizens. In these schemes, scammers impersonate law enforcement officials, CBI officers, Enforcement Directorate agents, Narcotics Bureau personnel and make video calls to unsuspecting victims. They wear uniforms, sit in mock 'police stations', display fake official documents, and speak in authoritative tones.
Once the victim is on the call, the scammers fabricate serious charges: drug trafficking, money laundering, and identity theft. They then 'digitally arrest' the victim, demanding that the person remain visible on the video call always and not communicate with anyone else until a'settlement' is reached. Victims, gripped by fear and legal ignorance, often comply for hours, days, or even weeks.
According to The Wire, Indians lost Rs... 1,935 crore to digital arrest scams in 2024 alone, approximately 20 times the losses recorded in 2022. In just the first two months of 2025, 17,718 such incidents were reported, with victims losing Rs.. 210.21 crore.
The victims are not naive or uneducated. An 86-year-old woman from South Mumbai lost over Rs. 20 crore over two months. A 77-year-old Noida resident was 'arrested' digitally for 16 days, losing Rs. 3.14 crore. The psychological weaponisation of official authority makes these scams extraordinarily effective across all demographics. As cyber law specialist Jayesh Bhandarkar has clearly stated, there is no concept of a 'digital arrest' in Indian law. Every genuine arrest requires a warrant and in-person execution.
2. India's Rs. 30,000+ Crore Bank Fraud Crisis: A Decade of Escalating Losses
The digital house arrest phenomenon is just one face of India's larger cybercrime emergency. When we zoom out to look at the financial sector, the numbers are even more sobering. Bank frauds in India exceeded Rs 30,000 crore in FY23, and over the last decade, financial fraud losses have cumulatively crossed Rs.. 4.69 trillion, a figure that underscores the systemic vulnerability of our banking and payment infrastructure.
Digital payment fraud cases of Rs. 1 lakh and above increased 11 times since 2020-21, while the total money involved rose 12 times over the same period. The Reserve Bank of India reported 29,082 such cases in 2023-24, involving Rs. 1,457 crore. These are not abstract statistics; behind every number is a family's savings, a business's working capital, or a retiree's life earnings, wiped out in seconds.
A particularly alarming dimension is the organised, transnational nature of modern cybercrime. Reports indicate that 46% of cyber frauds in early 2024 originated from Cambodia, Laos, and Myanmar, where Chinese crime syndicates operate massive, industrialised cybercrime centres staffed with trafficked workers. These operations use call centres, mule bank accounts, fake SIM cards, and inter-state networks in a coordinated fashion, making detection and disruption extremely complex.
3. Understanding Data Encryption: India's First Line of Digital Defence
At the heart of any credible cybersecurity strategy lies data encryption, the process of Converting readable data into an unreadable encoded format that can only be decoded by authorised parties possessing the correct key. In the context of India's escalating fraud landscape, data encryption is not merely a technical safeguard; it is a fundamental act of institutional responsibility.
Encryption operates across multiple layers of digital infrastructure. At rest, it protects stored data on servers, devices, and databases from being accessed even if the physical hardware is stolen or compromised. In transit, it secures data as it travels across networks, preventing interception by malicious third parties. End-to-end encryption, used in secure messaging applications, ensures that only the communicating parties can read the messages.
For Indian enterprises, the stakes are especially high. About 83% of Indian organisations face cyber threats every year, yet only 24% are adequately prepared to face them. Ransomware attacks, which work by encrypting a victim's own data and demanding ransom for the decryption key, have evolved from simple file-locking tools to sophisticated multi-pronged extortion campaigns that also threaten to publicly release stolen data. The 2023 ransomware attack on AIIMS Delhi and the IDFC First Bank breach of the same year illustrate how even premier institutions remain vulnerable.
The key encryption standards relevant to Indian businesses include AES-256 (the gold standard for symmetric encryption), RSA for secure key exchange, and TLS/SSL protocols for securing web communications. As quantum computing advances, forward-looking organisations must also begin transitioning to quantum-resistant encryption algorithms, a shift that the Indian government and security experts have already begun advocating.
AES-256 Encryption: The globally accepted benchmark for securing sensitive data at rest and in transit.
TLS/SSL Protocols: Essential for securing all web-based communications, e-commerce, and banking transactions.
End-to-End Encryption: Protects communication channels from interception by any third party, including service providers.
Quantum-Resistant Algorithms: The next frontier for Indian enterprises as quantum computing capabilities advance globally.
4. Cybersecurity Awareness Training: The Human Firewall India Desperately Needs
Even the most advanced technical defences can be circumvented if the human element is not addressed. Cybersecurity awareness training, the structured education of employees and citizens about digital threats, safe practices, and response protocols, is today considered the single most impactful investment an organisation can make in its security posture.
Consider this: a Phishing attacks have become hyper-personalised, drawing on data leaked from social media and corporate breaches to craft convincing fraudulent communications. Without trained employees who can recognise these attempts, even the best technical systems will eventually be compromised.
Effective cybersecurity awareness programmes for Indian organisations should cover several critical domains. Phishing recognition is fundamental; employees must learn to scrutinise email addresses, verify unexpected requests through secondary channels, and never click links from unverified sources. Understanding social engineering tactics, including digital arrest-style psychological pressure, is equally important. Password hygiene, multi-factor authentication adoption, and secure device management form the practical foundation of day-to-day digital safety.
Organisations should also conduct regular simulated phishing exercises, sending fake phishing emails to their own staff to measure vulnerability and reinforce learning. As brand shield demonstrates, organisations that run continuous, behaviour-based security training programmes see lower rates of successful phishing attacks compared to those relying on annual compliance-based training alone.
India's cybersecurity skills shortage is a parallel crisis: with only 24% of organisations prepared for cyberattacks, the demand for trained cybersecurity professionals far outstrips supply. Investing in internal awareness training is thus both a security measure and a talent development strategy.
For Indian businesses, a robust cybersecurity awareness training programme should include:
Quarterly simulated phishing and social engineering exercises
Role-specific training modules for finance, HR, and IT personnel who are the highest-risk targets
Clear incident reporting protocols so employees know exactly what to do when they suspect a breach
Executive-level training, since C-suite members are increasingly targeted by Business Email Compromise (BEC) and 'digital arrest' style coercion

5. Asset Performance Management: The Overlooked Cybersecurity Dimension
When we discuss organisational resilience in India's threat landscape, Asset Performance Management (APM) may not immediately come to mind alongside encryption and awareness training. Yet its relevance is profound and increasingly acknowledged by security practitioners.
APM, as comprehensively detailed in refers to the systematic approach to monitoring, managing, and optimising the performance, reliability, and lifecycle of physical and digital assets within an organisation. In the cybersecurity context, this extends powerfully to IT asset management, the disciplined tracking and maintenance of all hardware, software, and network components that make up an organisation's digital infrastructure.
The connection between APM and cybersecurity is more direct than many realise. Unpatched software, obsolete hardware running unsupported operating systems, shadow IT (unauthorised devices connected to corporate networks), and expired security certificates are all asset management failures that directly translate into cybersecurity vulnerabilities. Threat actors actively scan for these weaknesses.
In India's industrial and enterprise sectors, APM also encompasses the protection of Operational Technology (OT) systems, the physical machinery and control systems used in manufacturing, energy, transportation, and utilities. As these systems become increasingly connected through the Internet of Things (IoT), they create new attack surfaces that malicious actors can exploit. The MiCODUS MV720 GPS tracker vulnerability affecting devices across 169 countries, including sensitive government fleets, is a stark reminder of how physical asset vulnerabilities can have catastrophic consequences.
IT Asset Inventory Management: Maintaining a complete, real-time inventory of all hardware, software, and network assets to identify unauthorised or vulnerable components.
Patch Management: Systematically applying security patches and updates across all assets to eliminate known vulnerabilities before they can be exploited.
End-of-Life Asset Decommissioning: Promptly retiring and securely disposing of assets that no longer receive security support from vendors.
Performance Monitoring & Anomaly Detection: Using APM tools to identify unusual system behaviour that may indicate a breach or ransomware activity in progress.
OT/IoT Security: Extending cybersecurity protocols to operational technology and connected devices that increasingly form part of India's critical infrastructure.
6. India's Institutional Response: I4C, DoT, and Microsoft Collaboration
India has not been passive in the face of this onslaught. The Indian Cyber Crime Coordination Centre (I4C), established by the Ministry of Home Affairs in 2020, has emerged as the nerve centre of India's national cybercrime response. Operating the National Cybercrime Reporting Portal (cybercrime.gov.in), the Citizen Financial Cyber Fraud Reporting and Management System (CFCFRMS), and the helpline 1930, I4C has saved over Rs. 5,489 crore from being syphoned off through coordinated freezing of fraudulent transactions.
One of I4C's most significant recent actions was its collaboration with Microsoft. I4C, in collaboration with Microsoft, blocked more than 1,000 Skype IDs involved in blackmail, extortion, and digital arrest fraud. In May 2025, the CBI, working with Microsoft's Digital Crimes Unit, executed raids at 19 locations across India, dismantling cybercrime networks impersonating Microsoft and targeting older adults in Japan. Six key operatives were arrested, two illegal call centres were shut, and critical digital infrastructure was seized.
The Department of Telecommunications (DoT) has been equally proactive. Its Digital Intelligence Platform (DIP) a secure bi-directional information sharing system now connects 620+ organisations, including banks, telecom operators, and law enforcement agencies, enabling real-time identification of fraudulent SIM activations and spoofed calls. The DoT's Chakshu facility, part of the Sanchar Saathi initiative, allows citizens to report suspected fraud communications before any financial loss occurs. In 2025 alone, over 5.19 lakh reports were received through Chakshu, covering KYC frauds, impersonation of government agencies, and investment scams.
The I4C has blocked more than 9.4 lakh SIM cards and over 2.6 lakh IMEI numbers based on police reports, while 3,962 Skype IDs and 83,668 WhatsApp accounts linked to digital arrest frauds have been shut down.
7. AI-Driven Fraud: The Technological Arms Race in India's Cybercrime Theatre
Perhaps the most alarming development in India's cybersecurity landscape is the rapid weaponisation of Artificial Intelligence by criminal actors. AI-generated fake calls now convincingly replicate the voices of family members, bank officials, and government representatives. Deepfake video technology produces scammers who are visually indistinguishable from real officials. Automated AI systems can generate and dispatch thousands of personalised phishing messages per hour, dramatically scaling the reach of fraud operations.
In 2024, approximately 80% of phishing campaigns targeting India incorporated AI-generated content. Criminals are also using AI to automate the identification of high-value targets, analyse social media profiles to craft personalised social engineering attacks, and adapt their tactics in real time based on a victim's responses. The extortion via video conferencing model central to digital house arrest scams has been turbocharged by deepfake technology that makes fake police stations and uniforms completely convincing.
India's response to this threat has included investment in AI-powered defensive tools. Zero Defend Security launched Vastav AI in March 2025, India's first deepfake detection system, claiming 99% accuracy using machine learning, forensic analysis, and metadata inspection. The I4C's Threat Analytics Unit uses AI and data pattern recognition to identify organised cybercrime networks across state boundaries.
8. How to Report Cyber Fraud in India: Your Toolkit for Defence
When it comes to cybercrime in India, every minute matters. The faster a fraud is reported, the higher the probability of recovering stolen funds. The government has built a structured ecosystem for reporting, and understanding it could make a critical difference in a crisis.
National Cyber Crime Helpline 1930: Dialling 1930 immediately after a fraud connects you to the Citizen Financial Cyber Fraud Reporting and Management System, which can trigger real-time coordinated action across banks and payment systems to freeze stolen funds. Early reporting via this channel has contributed to the recovery of over Rs. 5,489 crore so far.
National Cybercrime Reporting Portal cybercrime.gov.in: The portal accepts complaints on all categories of cybercrime, including financial fraud, hacking, online harassment, and crimes against women and children. Complaints feed into the I4C's analytical systems, including the Pragmatism geospatial mapping module. Every report contributes to the identification and arrest of criminal networks.
Chakshu Portal San char Saathi: Specifically designed for reporting suspected fraud communications scam calls, fraudulent SMS, or suspicious messages where no financial loss has yet occurred. Chakshu reports allow DoT to analyse telecom misuse patterns and block fraudulent numbers before they claim more victims. In 2025, Chakshu has already received over 5.19 lakh such prevention-focused reports.
Remember: No government agency, CBI officer, Enforcement Directorate official, or court will ever demand money, conduct arrests, or ask you to stay on a video call via Skype or WhatsApp. If you receive such a call, disconnect immediately and report to 1930 or cybercrime.gov.in.
9. Building an Integrated Cybersecurity Strategy for Indian Organisations
The three pillars we have examined are data encryption, cybersecurity awareness training, and asset performance management are not independent measures. Their real power lies in integration. An organisation that encrypts its data without training its people will be undone by a phishing attack that delivers ransomware capable of bypassing technical controls. A well-trained workforce operating on unpatched, unmonitored assets will remain vulnerable to automated attacks that exploit known vulnerabilities.
For Indian enterprises, we recommend building a holistic cybersecurity framework that addresses all three dimensions simultaneously:
Encrypt Everything: Implement end-to-end encryption for all sensitive data at rest and in transit. Adopt AES-256 as the minimum standard and begin evaluating quantum-resistant alternatives for future-proofing.
Train Continuously: Replace annual compliance-based training with a continuous, behaviour-based security awareness programme that adapts to emerging threats like AI-generated phishing and deepfake scams.
Manage All Assets: Maintain a real-time inventory of all IT and OT assets, enforce rigorous patch management, decommission end-of-life hardware, and extend security monitoring to all IoT-connected devices.
Test Regularly: Conduct penetration testing, red team exercises, and simulated phishing campaigns at least quarterly to identify gaps before adversaries do.
Plan for Breach: Develop and rehearse an incident response plan. Cybersecurity is as much about minimising impact when a breach occurs as it is about preventing one.
Comply Proactively: Stay ahead of India's DPDPA requirements, RBI cybersecurity mandates, and sector-specific compliance frameworks. Regulatory penalties are increasingly significant, but reputational damage from a breach is often far more costly.
10. The DPDPA 2023 and Regulatory Compliance: What Indian Businesses Must Know
India's Digital Personal Data Protection Act (DPDPA) 2023 represents a watershed moment in the country's data governance landscape. For the first time, India has a comprehensive, cross-sector legal framework governing the collection, processing, storage, and transfer of personal data placing obligations on businesses that match global standards like Europe's GDPR.
The DPDPA places specific data security obligations on organisations. Data fiduciaries entities that determine the purpose and means of processing personal data must implement reasonable security safeguards, including technical measures like encryption to prevent data breaches. In the event of a breach, mandatory notification to affected individuals and to the Data Protection Board is required. Non-compliance carries significant financial penalties.
For Indian IT and BFSI sectors, which handle vast volumes of personal and financial data, the DPDPA is not merely a compliance exercise it is a catalyst for comprehensive data security transformation. Implementing robust data encryption, conducting regular security audits, training staff on data handling obligations, and maintaining meticulous asset records are all foundational requirements for DPDPA compliance that also directly strengthen organisational cybersecurity posture.
11. Special Sectors at Risk: BFSI, Healthcare, and Critical Infrastructure
While every sector faces cybercrime threats, certain industries in India face disproportionate exposure due to the sensitivity of the data they handle and the critical nature of the services they provide.
Banking, Financial Services, and Insurance (BFSI): As the primary target of digital fraud, bank fraud, and investment scams, the BFSI sector must operate at the highest level of cybersecurity maturity. The RBI's evolving cybersecurity framework, including the mandatory implementation of the Financial Fraud Risk Indicator (FRI), represents an important baseline, but leading institutions are going significantly further with AI-powered fraud detection, zero-trust network architectures, and real-time transaction monitoring.
Healthcare: The AIIMS ransomware attacks demonstrated the life-or-death stakes of healthcare cybersecurity. Patient data is among the most sensitive personal information in existence, and healthcare systems including connected medical devices represent high-value targets. Implementing robust encryption for patient records, rigorous access controls, and regular security audits is non-negotiable.
12. Key Takeaways
India's cybercrime crisis demands a comprehensive, integrated response; no single solution is sufficient.
Digital House Arrest is a real and growing threat: Scammers using AI-generated calls, deepfakes, and video conferencing to impersonate law enforcement have defrauded thousands of Indians. There is no legal concept of 'digital arrest' in India.
The financial toll is staggering: Rs. 22,845 crore lost to cyber fraud in 2024 (a 206% year-on-year increase), with the decade's total bank fraud losses crossing Rs. 4.69 trillion.
Data encryption is foundational: AES-256 encryption, TLS/SSL protocols, and end-to-end encryption are essential defences against data breaches, ransomware, and interception. Quantum-resistant encryption is the next frontier.
Cybersecurity awareness training is the human firewall: Continuous, behaviour-based training programmes, not annual compliance tick-boxes, are what effectively protect organisations from phishing, social engineering, and AI-generated fraud.
Asset Performance Management closes the technical gap: Unpatched software, obsolete hardware, and unmonitored IoT devices are open doors for cybercriminals. Rigorous APM practices are a cybersecurity imperative.
India's institutional response is strengthening: I4C's collaboration with Microsoft (blocking 1,000+ Skype fraud IDs), DoT's Chakshu portal, and the Digital Intelligence Platform represent significant systemic advances.
Report immediately: Call 1930 or visit cybercrime.gov.in immediately after any cyber fraud. Use the Chakshu portal on Sanchar Saathi to report suspected scam communications before financial loss occurs.
Conclusion: Building a Truly Secure Digital India
The battle for India's digital future is being fought on multiple fronts simultaneously. Criminal networks operating from Southeast Asian scam hubs, armed with AI tools and deep knowledge of Indian psychological vulnerabilities, are confronting citizens and enterprises whose awareness and defences often lag far behind the threat.
We believe that the path forward is neither fatalism nor panic it is informed, systematic action. Data encryption protects the assets we build. Cybersecurity awareness training equips the people who build them. Asset performance management ensures the systems we rely on remain secure and resilient. Together, these three pillars form the foundation of an organisational cybersecurity posture adequate for India's current threat environment.
The government's initiatives, from I4C's real-time fraud response to DoT's Digital Intelligence Platform and the Chakshu portal, provide critical infrastructure for the national response. But institutional measures alone are insufficient. Every enterprise must make cybersecurity investment a board-level priority. Every employee must become a trained and vigilant participant in organisational defence. And every citizen must understand that a phone call from someone claiming to be a police officer and demanding they stay on a video call is not law; it is fraud.
Frequently Asked Questions (FAQ)
Q: What is a 'Digital House Arrest' and how can I identify it?
A: A Digital House Arrest is a scam where fraudsters impersonate law enforcement officials (CBI, ED, police) via video call, fabricate serious charges against you, and demand you remain visible on screen while paying money to avoid fake legal consequences. You can identify it because no legitimate Indian law enforcement agency conducts arrests, investigations, or extracts payments via video calls or phone. If you receive such a call, disconnect immediately and report to 1930 or cybercrime.gov.in.
Q: Why is data encryption particularly important for Indian businesses right now?
A: India's DPDPA 2023 now legally mandates reasonable security safeguards including encryption for all personal data. Beyond legal compliance, with cyberattacks costing Indian organisations a record Rs 22,845 crore in 2024 and ransomware now encrypting corporate data as an extortion weapon, encryption represents your organisation's most fundamental technical defence against both external attackers and insider threats.
Q: What should a good cybersecurity awareness training programme for Indian employees include?
A: An effective programme should include phishing recognition training with simulated phishing exercises, education on social engineering tactics (including digital arrest-style psychological pressure), password hygiene and MFA adoption guidance, secure device and data handling protocols, incident reporting procedures, and specific training on AI-generated fakes and deepfakes. Training should be continuous and behaviour-based, not a single annual compliance exercise.
Q: How does Asset Performance Management relate to cybersecurity?
A: APM in the cybersecurity context means systematically tracking, patching, monitoring, and decommissioning all IT and operational assets. Unpatched software, unsupported hardware, and unmonitored IoT devices are among the most common entry points for cyberattacks. Rigorous asset management closes these gaps systematically, reduces the attack surface, and ensures that anomalous system behaviour, a potential indicator of breach, is detected quickly.
Q: What should I do immediately if I fall victim to a cyber fraud in India?
A: Act immediately: (1) Call the National Cyber Crime Helpline at 1930 this can trigger real-time coordination to freeze stolen funds. (2) File a complaint at cybercrime.gov.in. (3) Contact your bank directly through official channels to report the fraud and request an emergency freeze on suspicious transactions. (4) Preserve all evidence screenshots, transaction IDs, call records, and messages. Speed is critical every minute improves your chances of fund recovery.
Q: What is the Chakshu portal and who should use it?
A: Chakshu is a facility under the Department of Telecommunications' Sanchar Saathi initiative. It is specifically designed for reporting suspected fraud communications suspicious calls, SMS, or messages where no financial loss has yet occurred. If you receive what seems like a scam call or fraudulent message, report it on Chakshu before it claims another victim. In 2025, over 5.19 lakh such reports have already been received, helping DoT identify and block fraudulent telecom resources.
Q: How is I4C working with technology companies to fight cybercrime?
A: I4C has collaborated with Microsoft to block over 1,000 Skype IDs used in digital arrest scams and blackmail. The CBI, working with Microsoft's Digital Crimes Unit and Japan's Cybercrime Control Center (JC3), conducted raids at 19 locations in May 2025 to dismantle tech support fraud networks. I4C also works with banks, NPCI, telecom operators, and international agencies through the Digital Intelligence Platform and Joint Cybercrime Coordination Teams to enable real-time fraud detection and cross-border takedowns.

